Privileged Access Management (PAM) controls for cyber insurance
Quickly demonstrate Privileged Access Management best practices to cyber insurance providers
Challenge
The cyber insurance industry expects you to have PAM best practices in place before they grant a policy.
Risk
If you can’t demonstrate PAM policies and procedures, you may not be able to obtain or renew your policy.
Solution
When providers see you have the industry-leading PAM solution, they grant and renew policies faster.
Obtain cyber insurance to transfer your risk
Almost 70% of organizations are currently investing in insurance and just under 20% are considering cyber insurance to improve their cyber resilience, according to Delinea research. Insurance carriers and brokers are doing their best to calculate your cyber risk, so they can offer policies with appropriate terms and costs. As part of the insurance application process, expect surveys and interviews with cyber experts, asking for evidence that your security controls are in place and working as expected.
Download our sample Cyber Insurance Readiness Checklist—it guides you through the top questions most insurance companies ask when you apply for cyber insurance.

Protect privileged access and manage enterprise passwords
Secret Server gives you the capabilities to automatically discover, manage, protect, and audit privileged account access. With the industry-leading Privileged Access Management (PAM) vault at the core, Secret Server manages all types of secrets and privileged credentials, including passwords and SSH keys for domain administrators, application accounts, database accounts, third parties, and business users.
Reporting is a also crucial component of demonstrating compliance to insurers that want to see at-a-glance how well policies are followed and where there are exceptions. Secret Server features help you meet these requirements and demonstrate compliance to satisfy insurers requirements. Out-of-the-box and easily customizable reporting features save time and make reviews and audits painless.

Enforce MFA on servers
Insurance companies know that cyber criminals seek to attack servers to exfiltrate sensitive data and negative impact operations, resulting in expensive fines and downtime. That’s why it’s important to show them how you can identify and contain server-based attacks, with MFA at the server level and restrictions on privilege elevation on servers.

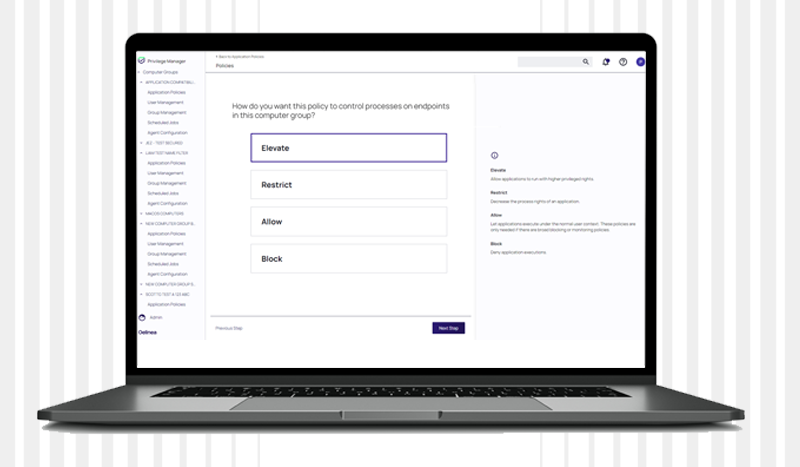
Manage workstation privileges with application control
Insurance companies want to understand how you’ll deal with phishing attacks that could install malware and ransomware on endpoints like business user machines. Show them how you eliminate local administrator accounts and create allow, deny, and restrict lists to help prevent workstation-based attacks.
Govern service accounts from start to finish
Account Lifecycle Manager ensures proper access governance of your service accounts. You can discover, secure, provision, and decommission service accounts without worrying that you’re breaking dependencies or impacting uptime.

Need to demonstrate compliance for cyber insurance?
This curated collection of resources prepares you for cyber insurance negotiations.
Get these must-have resources:
- Conversational Geek’s Guide to Cyber Insurance
- Cyber Insurance Survey Results from 300 IT Decision-Makers
- Cyber Insurance Readiness Checklist
- Privileged Account Discovery Tool for Windows
Privileged Access Management Solutions for Cyber Insurance
Full-featured, free trials get you up and running fast
Secret Server
Vault credentials, ensure password complexity, and delegate role-based access.
Server PAM
Privilege Manager
Privileged Behavior Analytics
Increase accountability and oversight of privileged sessions.
Account Lifecycle Manager
Seamless service account governance from discovery and provisioning through decommissioning.
